Which of the Following Best Describes Residual Risk
The level of risk before security measures are applied C. Threats vulnerability asset value residual risk B.
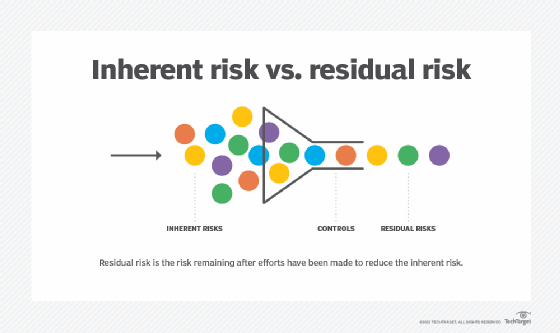
What Is Residual Risk How Is It Different From Inherent Risk
Which of the following best describes residual risk.

. Ad di hp 19. The categorization after mitigation and residual risk assessmentD. Risk exposure Kindly be reminded that the suggested answer is for your reference only.
Risk that affects a large number of assets C. Which of the following best describes the meaning of Initial Level of Risk in Risk Management. The level of risk before security measures are applied C.
An inherent risk can be defined as the difference between the risk response benefit and the residual risk produced by the particular risk response. The categorization after implementation of mitigating actions C. Residual Risk Threats x Vulnerability x Asset Gap x Control Gap.
Management should treat risks until the residual risk equals the inherent risk. It doesnt matter whether you have the right or. Risks that still remain after implementing a risk response.
Financial outcomes are one of the methods for measuring potential value for taking a risk. An individual securitys total risk B. Which best defines residual risk.
The categorization before determining and implementing mitigating actionsE. An analytical method that simulates a real-life system for risk analysis. Which of the following best describes a Monte Carlo simulation.
Reject the risk d. The categorization before risk identification. Management should act to lower risk until the costs of further treatment.
Total risk asset value countermeasures residual risk C -- 14. The level of risk after security measures are applied D. SLE frequency ALE which is equal to residual risk C.
The categorization after initial risk assessmentC. Measure residual risk b. The impact of risk if a threat is realized.
Which of the following BEST demonstrates to an IS auditor that an organization has implemented effective risk management processes. Which of the following is true of an inherent risk. A The likelihood of occurrence of a threat B The level of risk before security measures are applied C The level of risk after security measures are applied D The impact of risk if a threat is realized.
The utility of the risk describes the usefulness of a particular risk to an individual. Total risk asset value countermeasures residual risk. An inherent risk is the probability or likelihood of a risk occurring multiplied by the impact should it actually occur.
The likelihood of occurrence of a threat B. The Sarbanes Oxley act of 2002 significantly impacted the independent CPA audit. Threats vulnerability asset value controls gap residual risk D.
Residual Risk Threats x Exploit x Asset Value x Control Gap. Organizations identification and analysis of the risks that threaten the. Which of the following best describes residual risk.
Which of the following best describes the meaning of Initial Level of Risk in Risk ManagementA. Threats vulnerability asset value residual risk B. The categorization after initial risk assessment D.
Uncertainty likelihood or possibilityB. You are implementing security controls to mitigate threats. Which of the following is the highest risk.
Which of the following best describes residual risk. Effect consequence or impactC. Moreover the same risk can be utilized by two individuals in different ways.
Enterprise risk management is narrower than internal control and focuses on risk mitigation strategies across the enterprise. The PMBOK Guide defines Residual Risks as those risks which are expected to remain after the planned response of risk has been taken as well as those that have been deliberately accepted By Defination. The level of risk after security measures are applied D.
Which of the following relations correctly describes residual risk. The likelihood of occurrence of a threat B. How long before an investment will pay for itself.
The risk assessment component of internal control involves the. In this instance which of the following is the BEST course of action. Residual Risk Threats x Vulnerability x Asset Value x Control Gap.
The categorization after implementation of mitigating actionsB. Course Hero member to access this document. Risk that affects a large number of assets C.
Management should treat risks at least annually. Which of the following best describes the target you are treating. Very high impact with moderate likelihood b.
Mitigate the risk c. Internal audit functions assessment of control deficiencies. Threats vulnerability asset value control gap residual risk D.
Option-C is answer ie. Which of the following should George use to calculate the companys residual risk. Which of the following best describes why companies should establish a written code of ethic.
It is considered a form of internal control The competition probably has one To comply with the securities and exchange commission To follow the DATA act. The impact of risk if a threat is realized. Management should act to reduce risks to the lowest possible.
An individual securitys total risk B. Which of the following statements best describes the principle of ALARP. The usefulness of the risk to individuals or groups.
The categorization after mitigation and residual risk assessment E. After a system risk assessment was performed it was found that the cost to mitigate the risk was higher than the expected loss if the risk was actualized. When you are assessing cybersecurity risks which activity comes first in the process.
Moderate impact with very high likelihood d. Moderate impact with high likelihood c. December 21 2021 What happens when you attempt to compile and run the following code.
Run a new risk assessment. Which of the following best describes ROI. Low impact with very high likelihood 10.
Enterprise risk management is narrower than internal control and focuses on managing the risk of loss resulting from external events. Independent outside auditors assessment of residual risk. December 14 2021 When residual risk is minimized.
Accept the risk b. Which one of the following describes systemic risk. Which of the following definitions best describes enterprise risk management.
Residual Risk Threats x Exploit x Asset Value x Control Gap. SLE frequency ALE which is equal to residual risk C. Upload your study docs or become a.

Residual Risk Examples How To Calculate Residul Risk

Comments
Post a Comment